Abstract
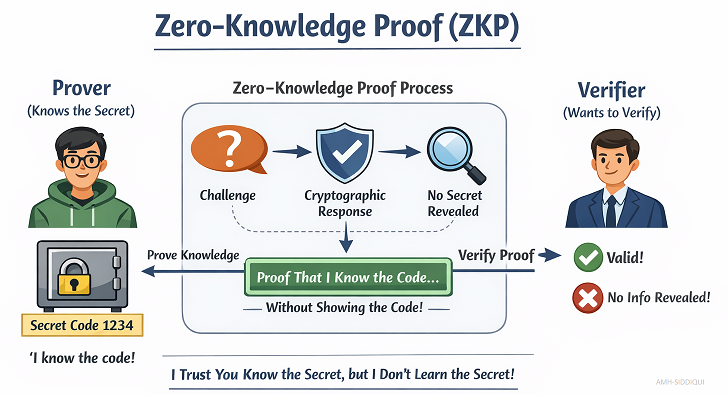
ZKP (Zero-Knowledge Proof) is a modern cryptographic concept that allows one party (the prover) to prove to another party (the verifier) that a statement is true without revealing any other information about it. In simple terms, ZKP lets someone prove they know something without actually sharing what they know. This powerful approach strengthens privacy, security, and trust in digital systems.
With the rise of blockchain, digital identity systems, and secure communications, ZKP has gained significant importance. This paper provides a comprehensive review of ZKP, including its explanation, key points, activation steps, use cases, dependencies, tools and technologies, and a conclusion highlighting its future potential.
Introduction
In today’s digital world, privacy and security are critical. Users want to prove their identity, verify transactions, or confirm information without exposing sensitive data. Traditional verification methods often require sharing personal information, passwords, or documents, which increases the risk of data breaches.
Zero-Knowledge Proof solves this problem. It allows verification without revealing the actual data. ZKP has applications in blockchain, finance, healthcare, voting systems, and more. This review paper explains ZKP in simple terms, highlighting its practical applications, and activation steps.
Explanation
Zero-Knowledge Proof is a cryptographic technique where:
- Prover: The person or system that wants to prove a fact.
- Verifier: The person or system that wants to confirm the fact.
The prover convinces the verifier that a statement is true without revealing the underlying information. For example. imagine a locked box with a secret key. The prover wants to show the verifier that they know the key without opening the box. They perform a series of interactions that convince the verifier they know the key, but the verifier never sees the key itself.
Types of ZKP
- Interactive ZKP: The prover and verifier exchange messages multiple times until the verifier is convinced.
- Non-Interactive ZKP: The proof is created once and can be verified by anyone without further interaction.
Key Features
- Completeness: If the statement is true, an honest verifier will be convinced by the proof.
- Soundness: If the statement is false, no prover can convince the verifier that it is true.
- Zero-Knowledge: No information other than the truth of the statement is revealed.
Key Points of ZKP
- Privacy Preservation: ZKP allows verification without revealing sensitive data.
- Security Enhancement: Reduces the risk of identity theft, fraud, or data leaks.
- Trust Building: Parties can interact securely even without trusting each other completely.
- Efficiency in Verification: ZKP can simplify complex verification processes in digital systems.
- Flexibility: Can be applied in various industries, including finance, healthcare, and blockchain.
General Activation Steps for ZKP
Activating or implementing ZKP in a digital system involves several key steps. For instance:
- Define the Statement to Prove – Identify the exact information that needs verification without revealing it. Example: A user wants to prove they are over 18 without showing their birthdate.
- Choose a ZKP Method – Select the appropriate type of ZKP, interactive or non-interactive, based on the use case.
- Generate the Proof: The prover uses cryptographic algorithms to generate a proof that can convince the verifier without revealing secret data.
- Verify the Proof: The verifier checks the proof using pre-defined cryptographic rules. If the proof is valid, the verifier is convinced the statement is true.
- Repeat or Store: Depending on the application, proofs can be temporary (for one-time verification) or stored (for later verification).
Use standardized cryptographic libraries to ensure the proof is secure and reliable.
Use Cases of ZKP – ZKP has numerous practical applications in real-world systems.
Blockchain and Cryptocurrencies:
- Privacy Coins – Cryptocurrencies like Zcash use ZKP to hide transaction details while proving their validity.
- Smart Contracts – ZKP can validate contract conditions without revealing the underlying data.
Digital Identity Verification
- Users can prove they meet certain criteria (age, citizenship, membership) without sharing full personal data.
- Reduces the risk of identity theft or data leaks.
Secure Voting Systems: Voters can prove they are eligible and that their vote counts without revealing the actual vote. Enhances election security and privacy.
Healthcare Data Sharing: Hospitals can prove patient eligibility for certain treatments without sharing full medical history. Ensures sensitive health data remains confidential.
Financial Services: Banks can verify creditworthiness or account balances without exposing full financial details. Helps in secure loan approvals and fraud prevention.
Dependencies
- Implementing ZKP requires attention to several dependencies:
- Mathematical Foundations: Understanding of cryptography, number theory, and modular arithmetic.
- Computational Resources: ZKP can be computationally intensive, requiring efficient algorithms and hardware.
- Secure Randomness: Many ZKP methods rely on random values to ensure security.
- Trusted Setup (Optional): Some ZKP systems require an initial setup phase to generate common parameters.
- Regulatory Compliance: ZKP implementations must follow privacy and security regulations relevant to the industry.
Platforms
- Blockchain Networks: Zcash, Ethereum (Layer 2 solutions), and Mina Protocol.
- Identity Management Systems: Platforms like Sovrin and Hyperledger Indy implement ZKP for secure digital identity.
Challenges in Implementing ZKP
Despite its advantages, ZKP faces several challenges:
- Complexity: Cryptographic algorithms behind ZKP are mathematically complex.
- Performance Overhead: Generating and verifying proofs can be resource-intensive.
- Integration: Integrating ZKP with existing systems may require significant changes.
- Regulatory Acceptance: New privacy-preserving methods may not yet be recognized by law in all regions.
- Trusted Setup Risks: Certain ZKP methods require a trusted setup, which could be a point of vulnerability if not properly managed.
Conclusion
Zero-Knowledge Proof is a groundbreaking cryptographic technique that allows secure verification without revealing sensitive information. Its applications span blockchain, finance, healthcare, voting, and digital identity systems. By preserving privacy and enhancing trust, ZKP is becoming increasingly relevant in today’s digital landscape.
While implementation can be complex, modern tools, libraries, and frameworks make it increasingly accessible. As privacy concerns grow and regulations tighten, ZKP will play a central role in creating secure and trustworthy digital systems.
Future Outlook
Wider adoption in decentralized finance (DeFi) and privacy-focused applications.
Integration with artificial intelligence (AI) for secure data processing.
Development of more efficient, scalable ZKP algorithms to reduce computational costs.
Zero-Knowledge Proof is no longer just a theoretical concept; it is a practical solution for real-world privacy and security challenges.
For further reading:
- EU GDPR – Article 13 (Information to Be Provided Where Personal Data Are Collected From the Data Subject)
- EU GDPR – Article 12 (Transparent Information, Communication, and Modalities for Exercising Data Subject Rights)
- EU GDPR – Article 11 (Processing Which Does Not Require Identification)
- EU GDPR – Article 10 (Processing Personal Data Related to Criminal Convictions and Offenses)
- EU GDPR – Article 9 (Processing Special Categories of Personal Data)
- EU GDPR – Article 8 (Conditions Applicable to Child’s Consent in Information Society Services)
- EU GDPR – Article 7 (Conditions for Consent)
- EU GDPR – Article 6 (Lawfulness of Processing)
- EU GDPR – Article 5 (Principles Relating to Processing of Personal Data)
- EU GDPR – Article 4 (Definitions)
- EU GDPR – Article 3 (Territorial Scope)
- EU GDPR – Article 2 (Material Scope)
- EU GDPR – Article 1 (Subject-matter and objectives)
- Why choose Virtual Learning?
- Benefits of Online Education
- Data Modeling – Identifiers / Keys
- Content Modeling – Controlled Vocabularies and Format
- Data Modeling – Arity of Relationships


