Abstract
EU GDPR Article 33 establishes a clear legal obligation for data controllers to notify the relevant supervisory authority of a personal data breach without undue delay and, where feasible, within 72 hours of becoming aware of it. The article also defines the responsibility of data processors to promptly inform controllers when a breach occurs. This provision plays a critical role in minimizing harm to individuals, ensuring transparency, and strengthening accountability in data protection practices. Article 33 emphasizes timely response, proper documentation, and risk-based decision-making when handling data breaches.
Explanation
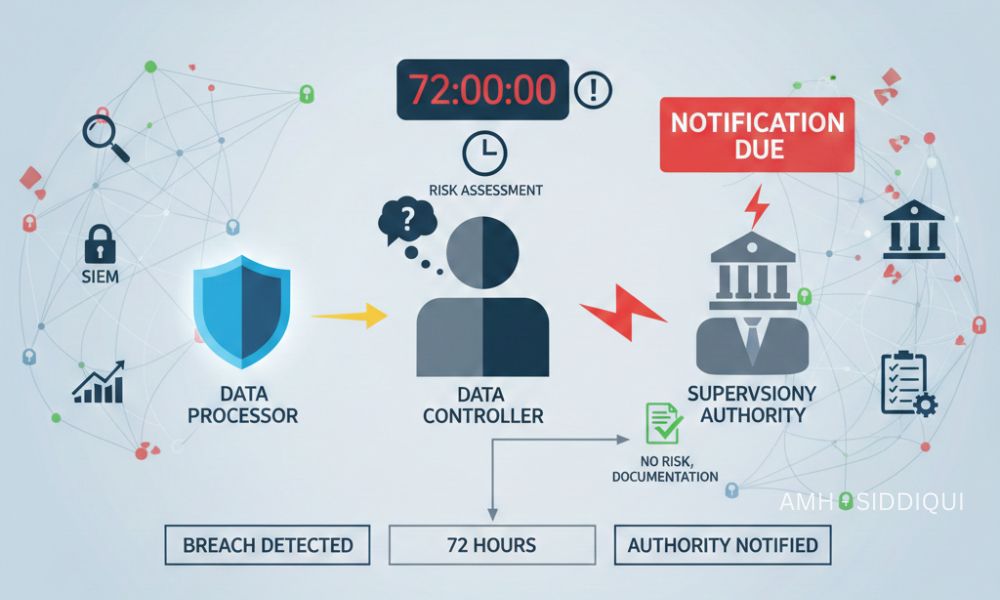
A personal data breach, under GDPR, refers to a security incident that leads to the accidental or unlawful destruction, loss, alteration, unauthorized disclosure of, or access to personal data. Article 33 specifically focuses on how and when such breaches must be reported to supervisory authorities.
According to this article, once a controller becomes aware of a personal data breach, they must assess whether the breach poses a risk to the rights and freedoms of natural persons. If there is any likelihood of risk, the controller must notify the supervisory authority within 72 hours. If the notification is delayed, the controller must provide reasons for the delay.
Importantly, not all breaches require notification. If the controller can demonstrate that the breach is unlikely to result in risk to individuals, notification is not mandatory. However, proper documentation is still required.
Processors, on the other hand, do not report directly to authorities. Their obligation is to inform the controller immediately after becoming aware of a breach, allowing the controller to meet the 72-hour deadline.
Key Points
- 72-Hour Rule: Controllers must notify the supervisory authority within 72 hours of becoming aware of a breach.
- Risk-Based Assessment: Notification is required only if the breach is likely to pose a risk to individuals.
- Processor Responsibility: Processors must notify controllers without undue delay.
- Content of Notification: Reports should include the nature of the breach, affected data, possible consequences, and mitigation measures.
- Delayed Notification: Any delay beyond 72 hours must be justified.
- Documentation Requirement: Even non-reportable breaches must be internally documented.
- Accountability Principle: Article 33 reinforces the GDPR principle that organizations must be able to demonstrate compliance.
General Activation Steps
To comply effectively with Article 33, organizations should follow a structured breach response process:
- Breach Detection and Identification: Implement systems and monitoring tools to quickly detect potential data breaches and security incidents.
- Initial Assessment: Determine whether personal data is involved and identify the scope, type of data, and number of individuals affected.
- Risk Evaluation: Assess whether the breach is likely to result in risks such as identity theft, financial loss, discrimination, or reputational damage.
- Internal Notification: Immediately escalate the incident to the Data Protection Officer (DPO) or designated compliance team.
- Notify the Supervisory Authority: If required, submit notification within 72 hours, even if all details are not yet available.
- Provide Additional Information: Supplement the notification as new facts emerge.
- Document the Breach: Maintain detailed internal records of the breach, actions taken, and decisions made.
Use Cases
- Cybersecurity Attack: A ransomware attack exposes customer email addresses and passwords. Since this data could be misused, the controller must notify the supervisory authority within 72 hours.
- Lost Employee Device: An unencrypted laptop containing employee personal data is stolen. Due to the potential risk of unauthorized access, notification is required.
- Misconfigured Database: A public cloud database accidentally exposes personal data for a short period. Even if no misuse is detected, the risk assessment may still trigger notification.
- Processor Incident: A third-party payroll provider suffers a breach. The processor must immediately notify the controller, who then evaluates reporting obligations.
- Low-Risk Incident: Encrypted data is accessed without the encryption key. If the controller determines there is no risk to individuals, notification may not be necessary, but documentation is still mandatory.
Dependencies
Article 33 does not operate in isolation. Its effectiveness depends on several interconnected GDPR provisions:
- Article 4 – Defines personal data and personal data breaches.
- Article 5 – Establishes principles like integrity and confidentiality.
- Article 24 – Requires controllers to implement appropriate technical and organizational measures.
- Article 28 – Defines processor obligations.
- Article 32 – Focuses on security of processing.
- Article 34 – Governs communication of breaches to affected individuals.
Together, these articles form a comprehensive framework for breach prevention, response, and accountability.
Tools and Technologies
Organizations rely on various tools to ensure compliance with Article 33:·
- Security Information and Event Management (SIEM): Detects and analyzes security incidents.
- Data Loss Prevention (DLP) Tools: Prevent unauthorized data access or transfer.
- Incident Response Platforms: Coordinate breach management workflows.
- Encryption Technologies: Reduce breach impact and notification requirements.
- Risk Assessment Tools: Evaluate breach severity and likelihood of harm.
- Compliance Management Software: Track notifications, documentation, and reporting deadlines.
Investing in the right technologies significantly improves an organization’s ability to respond within the 72-hour window.
Let’s Wrap
EU GDPR Article 33 is a cornerstone of data breach management and regulatory accountability. By enforcing strict timelines and clear responsibilities, it ensures that supervisory authorities can act swiftly to protect individuals’ rights and freedoms. The article also encourages organizations to strengthen internal security, adopt proactive monitoring, and develop well-defined incident response plans.
Compliance with Article 33 is not just about meeting deadlines, it’s about fostering trust, minimizing harm, and demonstrating responsibility in the digital age. Organizations that prepare in advance, train their teams, and leverage appropriate tools are far better positioned to handle breaches effectively and maintain GDPR compliance.
For further reading:
- EU GDPR – Article 32 (Security of Processing)
- EU GDPR – Article 31 (Cooperation with the Supervisory Authority)
- EU GDPR – Article 30 (Records of Processing Activities)
- EU GDPR – Article 29 (Processing Under the Authority of the Controller or Processor)
- EU GDPR – Article 28 (Processor)
- EU GDPR – Article 27 (Representatives of Controllers or Processors Not Established in the Union)
- EU GDPR – Article 26 (Joint Controllers)
- EU GDPR – Article 25 (Data Protection by Design and by Default)
- EU GDPR – Article 24 (Responsibility of the Controller)
- EU GDPR – Article 23 (Restrictions on Data Subject Rights)
- EU GDPR – Article 22 (Automated Individual Decision-Making, Including Profiling)
- EU GDPR – Article 21 (Right to Object)
- EU GDPR – Article 20 (Right to Data Portability)
- EU GDPR – Article 19 (Notification Obligation Regarding Rectification or Erasure of Personal Data or Restriction of Processing)
- EU GDPR – Article 18 (Right to Restriction of Processing)
- EU GDPR – Article 17 (Right to Be Forgotten)
- EU GDPR – Article 16 (Right to Rectification)

