Abstract
EU GDPR Article 34 focuses on one of the most critical aspects of data protection: transparent communication with individuals when their personal data is compromised. When a personal data breach is likely to result in a high risk to the rights and freedoms of natural persons, the data controller is legally required to inform affected data subjects without undue delay. This article explores Article 34 in detail, explaining its purpose, scope, practical application, and operational requirements. It also highlights real-world use cases, dependencies, and the tools organizations rely on to ensure compliance.
Explanation
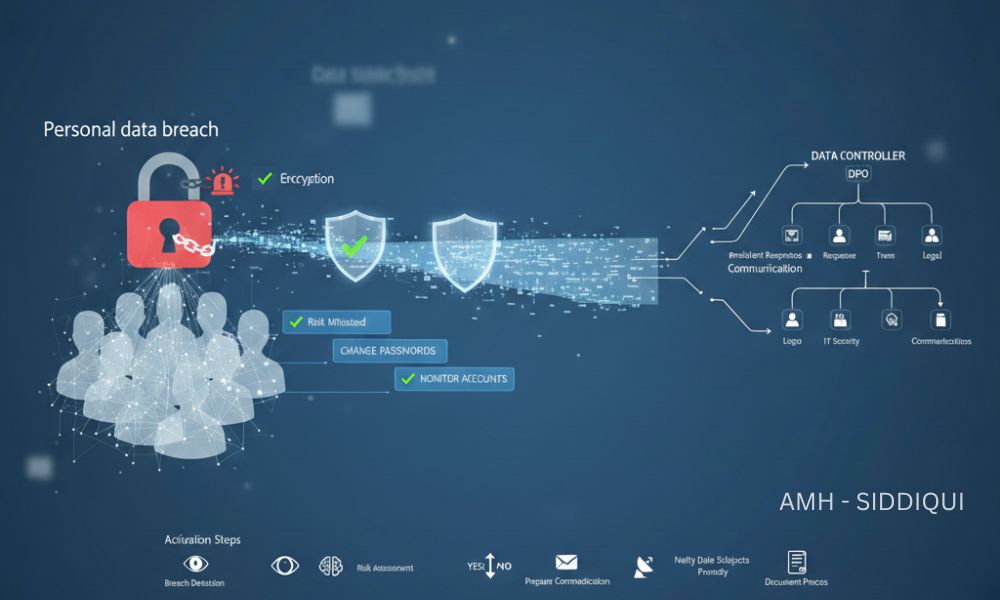
Article 34 of the General Data Protection Regulation (GDPR) addresses direct communication with data subjects following a personal data breach. While Article 33 focuses on notifying supervisory authorities, Article 34 shifts the emphasis to protecting individuals by ensuring they are informed promptly and clearly when a breach may put them at risk.The core objective of this article is harm prevention. By notifying data subjects in a timely manner, organizations enable individuals to take necessary precautions, such as changing passwords, monitoring accounts, or safeguarding against identity theft.
Importantly, not every data breach triggers Article 34. The obligation applies only when the breach is likely to result in a high risk to individuals’ rights and freedoms. If appropriate technical and organizational measures, such as strong encryption, were in place, or if subsequent actions have mitigated the risk, notification to data subjects may not be required.
Key Points
- Mandatory Communication: Controllers must inform data subjects when a breach poses a high risk.
- Without Undue Delay: Notifications must be issued as soon as reasonably possible.
- Clear and Plain Language: Communication must be easily understandable and free from technical jargon.
- Minimum Content Requirements: Notifications should describe:
- The nature of the breach
- Likely consequences
- Measures taken or proposed to address the breach
- Exceptions Apply: Notification may not be required if:
- Data was encrypted or rendered unintelligible
- Risk has been mitigated after the breach
- Individual notification would involve disproportionate effort (in which case public communication is allowed)
General Activation Steps
To comply with Article 34, organizations typically follow a structured response process:
- Breach Detection: Identify and confirm the occurrence of a personal data breach through monitoring systems or internal reporting.
- Risk Assessment: Evaluate whether the breach is likely to result in a high risk to data subjects’ rights and freedoms.
- Decision to Notify: Determine whether Article 34 notification requirements are triggered or whether an exception applies.
- Prepare the Communication: Draft a notification using clear, plain language, ensuring all mandatory elements are included.
- Notify Data Subjects Promptly: Deliver the communication through appropriate channels such as email, SMS, or official notices.
- Document the Process: Maintain internal records of the breach, assessment, and communication actions for accountability and audit purposes.
Use Cases
Article 34 is particularly relevant across multiple industries and scenarios, including:
- E-commerce Platforms: Exposure of customer login credentials or payment details requiring immediate user alerts.
- Healthcare Organizations: Breaches involving medical records that could impact patient privacy and well-being.
- Financial Institutions: Unauthorized access to banking or credit data posing risks of fraud or identity theft.
- Educational Institutions: Compromise of student personal information such as addresses, IDs, or academic records.
- Technology and SaaS Providers: Security incidents affecting user accounts, cloud storage, or communication platforms.
In each case, timely communication helps preserve trust and reduces the potential harm to individuals.
Dependencies
Compliance with Article 34 depends on several organizational and regulatory factors:
- Effective Incident Response Plans: Clearly defined breach response procedures ensure quick decision-making.
- Risk Assessment Frameworks: Organizations must be able to assess “high risk” consistently and objectively.
- Coordination with Article 33: Notification to supervisory authorities and data subjects often occur in parallel.
- Data Protection Officer (DPO) Involvement: The DPO plays a key role in advising on notification obligations and content.
- Internal Communication Channels: Smooth collaboration between IT, legal, compliance, and communications teams is essential.
Tools and Technologies
Modern organizations rely on various tools to support Article 34 compliance:
- Security Monitoring Systems: Detect anomalies, intrusions, and unauthorized access in real time.
- Incident Management Platforms: Track breach response activities and ensure deadlines are met.
- Encryption and Pseudonymization Tools: Reduce notification obligations by minimizing risk to data subjects.
- Customer Communication Systems: Enable rapid, large-scale notifications through secure and reliable channels.
- Compliance and Documentation Software: Maintain records required under GDPR’s accountability principle.
Let’s Wrap
EU GDPR Article 34 reinforces a fundamental principle of data protection: people have the right to know when their personal data is at serious risk. By requiring transparent, timely, and clear communication, the regulation places individuals at the center of breach response strategies.
For organizations, compliance with Article 34 is not just a legal obligation, it is an opportunity to demonstrate accountability, responsibility, and respect for user trust. With proper preparation, strong security measures, and well-defined response processes, controllers can meet their obligations while minimizing harm and reputational impact.In an era where data breaches are increasingly common, Article 34 serves as a vital reminder: how you respond matters just as much as how you protect data in the first place.
For further reading:
- EU GDPR – Article 33 (Notification of a Personal Data Breach to the Supervisory Authority
- EU GDPR – Article 32 (Security of Processing)
- EU GDPR – Article 31 (Cooperation with the Supervisory Authority)
- EU GDPR – Article 30 (Records of Processing Activities)
- EU GDPR – Article 29 (Processing Under the Authority of the Controller or Processor)
- EU GDPR – Article 28 (Processor)
- EU GDPR – Article 27 (Representatives of Controllers or Processors Not Established in the Union)
- EU GDPR – Article 26 (Joint Controllers)
- EU GDPR – Article 25 (Data Protection by Design and by Default)
- EU GDPR – Article 24 (Responsibility of the Controller)
- EU GDPR – Article 23 (Restrictions on Data Subject Rights)
- EU GDPR – Article 22 (Automated Individual Decision-Making, Including Profiling)
- EU GDPR – Article 21 (Right to Object)
- EU GDPR – Article 20 (Right to Data Portability)
- EU GDPR – Article 19 (Notification Obligation Regarding Rectification or Erasure of Personal Data or Restriction of Processing)
- EU GDPR – Article 18 (Right to Restriction of Processing)
- EU GDPR – Article 17 (Right to Be Forgotten)

