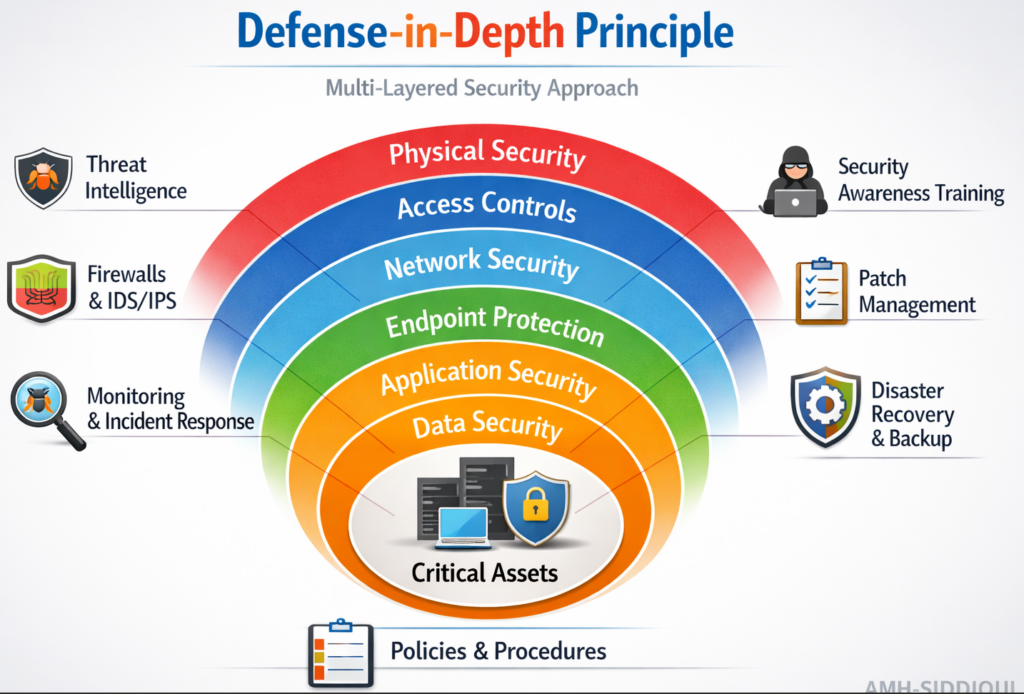
The Defense-in-Depth Principle is a cybersecurity strategy that emphasizes using multiple layers of security controls to protect systems, networks, and data. The core idea is that no single defense mechanism is foolproof; by combining multiple protective layers such as physical, technical, and administrative, organizations can reduce the likelihood and impact of security breaches. This approach mirrors military strategies where successive layers of defense increase resilience against attacks. Defense-in-depth is widely adopted in IT, critical infrastructure, and organizational security planning to create a robust, resilient security posture.
Defense-in-Depth operates on the premise that security should not rely on a single barrier. Instead, multiple layers of defense work together to provide redundancy and resilience. The layers typically include:
- Physical Controls: Safeguarding hardware and facilities through access controls, locks, CCTV, and environmental monitoring.
- Network Security Controls: Firewalls, IDS/IPS (Intrusion Detection/Prevention Systems), Network Segmentation, and VPNs (Virtual Private Networks).
- Endpoint Security: Anti-malware, patch management, device encryption, and secure configurations.
- Application Security: Input validation, secure coding practices, access controls, and application firewalls.
- Data Security: Encryption, secure storage, data masking, and backup/recovery mechanisms.
- Administrative/Operational Controls: Security policies, staff training, audits, incident response plans, and compliance with standards.
The principle is layered like an onion, where if one layer is penetrated, other layers still provide protection. It is both proactive, by preventing attacks, and reactive, by mitigating damage if an attack succeeds.
Benefits
- Minimized Single Point of Failure: Multiple layers prevent total system compromise.
- Reduced Risk of Breaches: Even if one layer is bypassed, others provide a safety net.
- Improved Incident Response: Layered monitoring allows quicker detection and response to attacks.
- Regulatory Compliance: Aligns with cybersecurity frameworks (such as ISO 27001, NIST, CIS Controls) and Data Regulations (like PDPL, GDPR, and CCPA).
- Holistic Security Posture: Covers technical, physical, and administrative aspects.
General Activation Steps
- Risk Assessment: Identify assets, threats, vulnerabilities, and potential impact.
- Layer Identification: Determine necessary layers such as physical, network, application, data, and policies.
- Control Implementation: Deploy security controls in each layer, e.g., firewalls, encryption, access control.
- Integration and Testing: Ensure layers work together without conflicts; test incident scenarios.
- Monitoring & Maintenance: Continuously monitor for breaches, update controls, and patch vulnerabilities.
- Training & Awareness: Educate staff about their role in maintaining layered security.
Dependencies
- Organizational Support: Commitment from management for investment in multiple layers.
- Skilled Personnel: Trained staff to implement, monitor, and respond effectively.
- Policy Framework: Well-defined policies and compliance requirements.
- Technology Infrastructure: Proper network, endpoint, and application capabilities.
- Regular Updates: Security controls and patches need consistent updating.
Key Challenges
- Complexity: Multiple layers increase management and operational complexity.
- Cost: Implementation and maintenance of several security layers can be expensive.
- Interdependency Issues: Poorly integrated layers may conflict or create gaps.
- Human Factor: Users may bypass controls or make errors, undermining security.
- Rapid Threat Evolution: Layers must adapt to new attack vectors and technologies.
Summary
The Defense-in-Depth principle is a cornerstone of modern cybersecurity, emphasizing redundancy, resilience, and layered protection. By combining physical, technical, and administrative controls, organizations can reduce the likelihood of security breaches and mitigate their impact. While implementation can be complex and resource-intensive, the benefits of a robust, multi-layered defense much more important than challenges. Defense-in-depth not only strengthens security posture but also enhances incident response and compliance capabilities, making it an essential strategy in protecting critical assets in today’s threat landscape.
For further reading:
- GDPR Aligned – Big Data Security Processes – Across the Data Lifecycle
- Zero-Knowledge Proof (ZKP) – A Professional Review
- Navigating the Big Data Lifecycle: From Collection to Insight
- EU GDPR – Article 13 (Information to Be Provided Where Personal Data Are Collected From the Data Subject)
- EU GDPR – Article 12 (Transparent Information, Communication, and Modalities for Exercising Data Subject Rights)
- EU GDPR – Article 11 (Processing Which Does Not Require Identification)
- EU GDPR – Article 10 (Processing Personal Data Related to Criminal Convictions and Offenses)
- EU GDPR – Article 9 (Processing Special Categories of Personal Data)
- EU GDPR – Article 8 (Conditions Applicable to Child’s Consent in Information Society Services)
- EU GDPR – Article 7 (Conditions for Consent)
- EU GDPR – Article 6 (Lawfulness of Processing)
- EU GDPR – Article 5 (Principles Relating to Processing of Personal Data)
- EU GDPR – Article 4 (Definitions)
- EU GDPR – Article 3 (Territorial Scope)
- EU GDPR – Article 2 (Material Scope)
- EU GDPR – Article 1 (Subject-matter and objectives)
- Why choose Virtual Learning?
- Benefits of Online Education
- Data Modeling – Identifiers / Keys
- Content Modeling – Controlled Vocabularies and Format
- Data Modeling – Arity of Relationships


