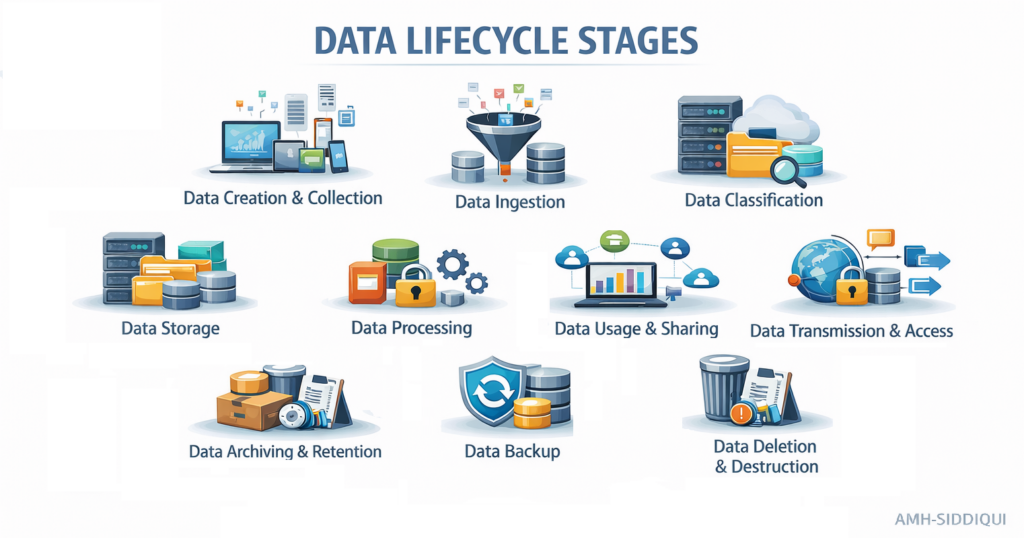
Data Creation & Collection: Data is first generated by users, applications, or digital systems and then collected from multiple sources. For example, when a user registers on an online platform, personal details such as name, email, and contact information are created and collected. In big data environments, this process produces massive volumes of information at high speed. From a privacy perspective, only necessary and relevant data should be created and collected, in line with the principle of data minimization and ensuring transparency, informed consent, and compliance with legal and ethical guidelines.
Data Ingestion: After data is collected, it must be transferred into appropriate systems through the process of data ingestion. This stage connects data collection with storage and processing environments such as cloud platforms or big data frameworks like Hadoop. Because ingestion often involves high-speed and high-volume data transfer, secure transmission mechanisms are critical. Protecting data during ingestion supports the principle of integrity and confidentiality, ensuring that data collected responsibly is not compromised in transit.
Data Classification: Once ingested, data must be organized through data classification to determine its sensitivity and required level of protection. Classification builds upon the ingestion process by assigning categories such as personal, sensitive, or non-sensitive data. In big data environments where multiple data types coexist, proper classification ensures that higher-risk information receives stronger safeguards. This step is essential for applying appropriate privacy controls and regulatory protections.
Data Storage: Classified data is stored for future access and use. Data storage systems, such as distributed databases or cloud infrastructures, hold large volumes of processed and unprocessed data. Since stored data remains vulnerable over time, strong encryption and access controls are required. Secure storage ensures continuity between processing and future usage while preserving confidentiality and integrity.
Data Processing: Following data storage, data enters the data processing stage, where it is cleaned, transformed, and analyzed to generate insights. Processing relies heavily on the structured organization established earlier. For example, customer data may be analyzed to detect fraud or improve services. To maintain privacy, organizations should minimize the use of personally identifiable information during processing, ensuring that analytical goals are achieved without unnecessary exposure of individual identities.
Data Usage & Sharing: Processed data is used for decision-making, analytics, or service improvement. It may also be shared internally or with external partners such as researchers or service providers. Sharing should follow privacy best practices, including anonymization or pseudonymization, to prevent exposure of personal identities. Usage must always align with defined and legitimate purposes.
Data Transmission & Access: As data moves across systems, transmission security is critical. Encryption ensures confidentiality during transfer between storage, processing, and sharing stages. Access control, such as role-based access control (RBAC), defines who can view or manipulate data, reducing the risk of internal misuse and enforcing accountability.
Data Backup:To safeguard data against loss or system failure, data backup is performed. Backups create secure copies of data that can be restored when needed. Since backups contain the same sensitive information as primary systems, they must follow the same privacy and security standards, including encryption and controlled access.
Data Archiving & Retention: Inactive or historical data is archived separately from active systems. Retention policies define how long data should be kept before deletion. These measures ensure compliance with legal and operational requirements while reducing privacy risks associated with indefinite storage.
Data Deletion & Destruction: When data is no longer required, it is removed from active systems (deletion) and permanently eliminated from all storage media (destruction). Proper execution ensures complete removal, preventing future misuse and closing the data lifecycle in a privacy-compliant manner.
For further reading:
- Zero-Knowledge Proof (ZKP) – A Professional Review
- EU GDPR – Article 13 (Information to Be Provided Where Personal Data Are Collected From the Data Subject)
- EU GDPR – Article 12 (Transparent Information, Communication, and Modalities for Exercising Data Subject Rights)
- EU GDPR – Article 11 (Processing Which Does Not Require Identification)
- EU GDPR – Article 10 (Processing Personal Data Related to Criminal Convictions and Offenses)
- EU GDPR – Article 9 (Processing Special Categories of Personal Data)
- EU GDPR – Article 8 (Conditions Applicable to Child’s Consent in Information Society Services)
- EU GDPR – Article 7 (Conditions for Consent)
- EU GDPR – Article 6 (Lawfulness of Processing)
- EU GDPR – Article 5 (Principles Relating to Processing of Personal Data)
- EU GDPR – Article 4 (Definitions)
- EU GDPR – Article 3 (Territorial Scope)
- EU GDPR – Article 2 (Material Scope)
- EU GDPR – Article 1 (Subject-matter and objectives)
- Why choose Virtual Learning?
- Benefits of Online Education
- Data Modeling – Identifiers / Keys
- Content Modeling – Controlled Vocabularies and Format
- Data Modeling – Arity of Relationships


